by Royal Cloud | Dec 20, 2025 | Cloud
Are you a bug bounty hunter on a mission to uncover vulnerabilities and secrets hidden within Amazon Web Services (AWS)? In the world of cybersecurity, AWS is a treasure trove for potential security issues, and today, I want to share my journey of discovery using two...
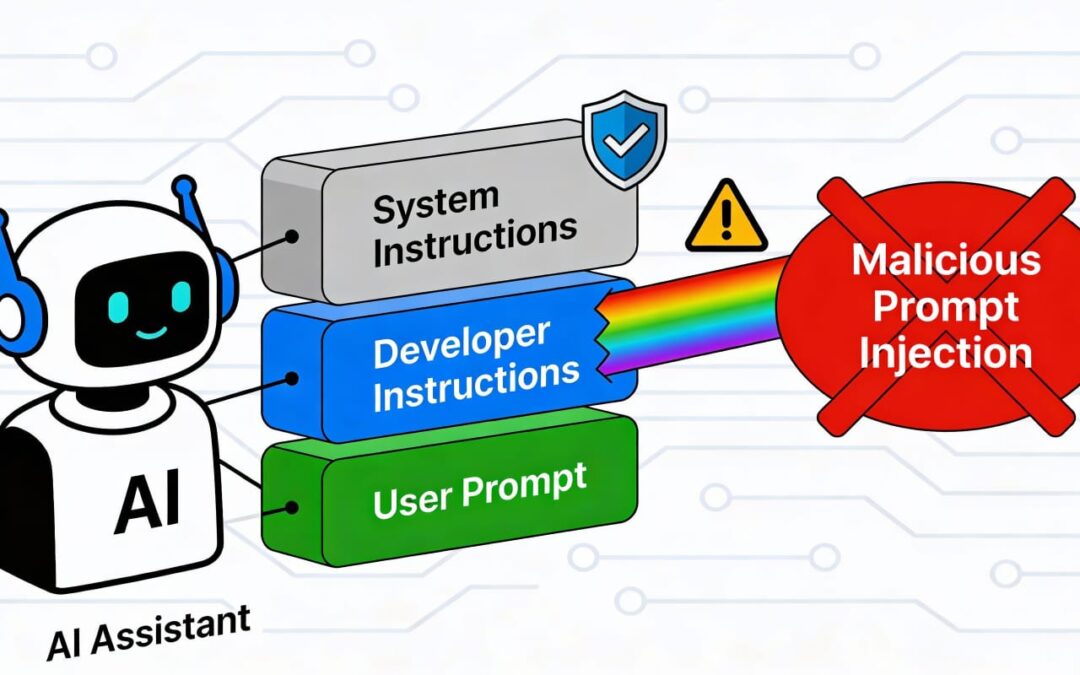
by Royal Cloud | Dec 16, 2025 | Cloud
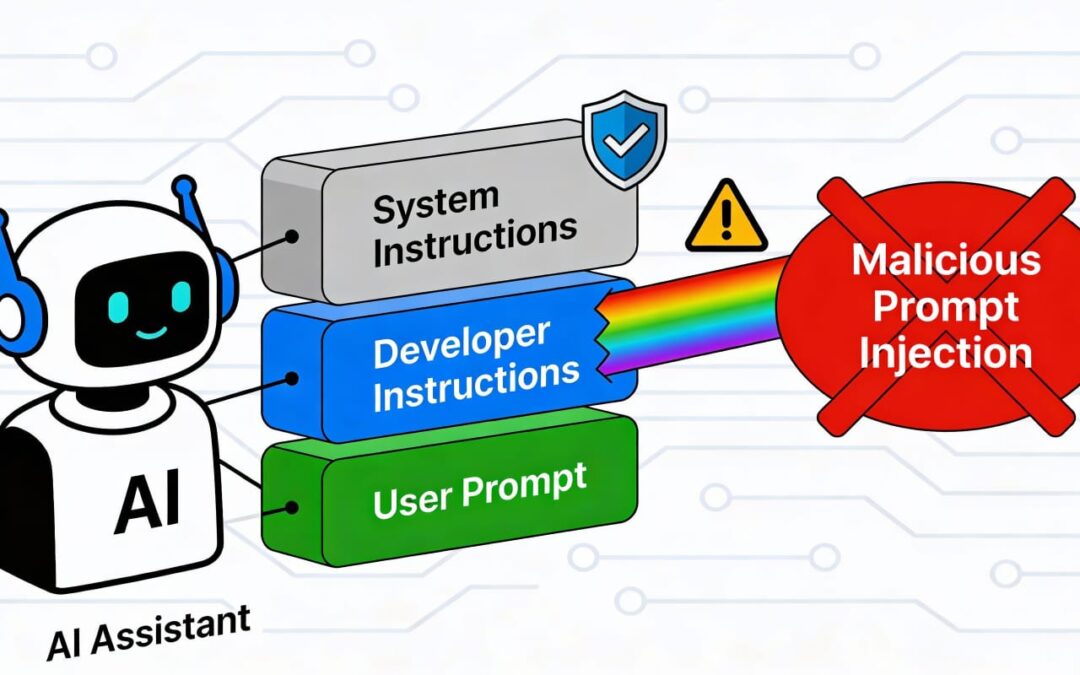
Prompt injection is a vulnerability that targets artificial intelligence (AI) models, particularly those trained in natural language processing (NLP) and large language models (LLMs). By crafting carefully designed inputs, attackers can manipulate AI systems to behave...

by Royal Cloud | Dec 16, 2025 | Cloud
In this day and age of hyper connected digital world where cyber-attacks grow at an exponential rate, organizations need to be more proactive in securing their vital assets. Threat modeling is recognized as a core activity in contemporary cybersecurity and is a...