by Royal Cloud | Dec 20, 2025 | Security
JS Enumeration is a crucial step in the process of identifying and exploiting vulnerabilities in a website. As a bug bounty hunter, you will need to be familiar with the different tools and techniques available to you for this purpose. In this article, we will take a...
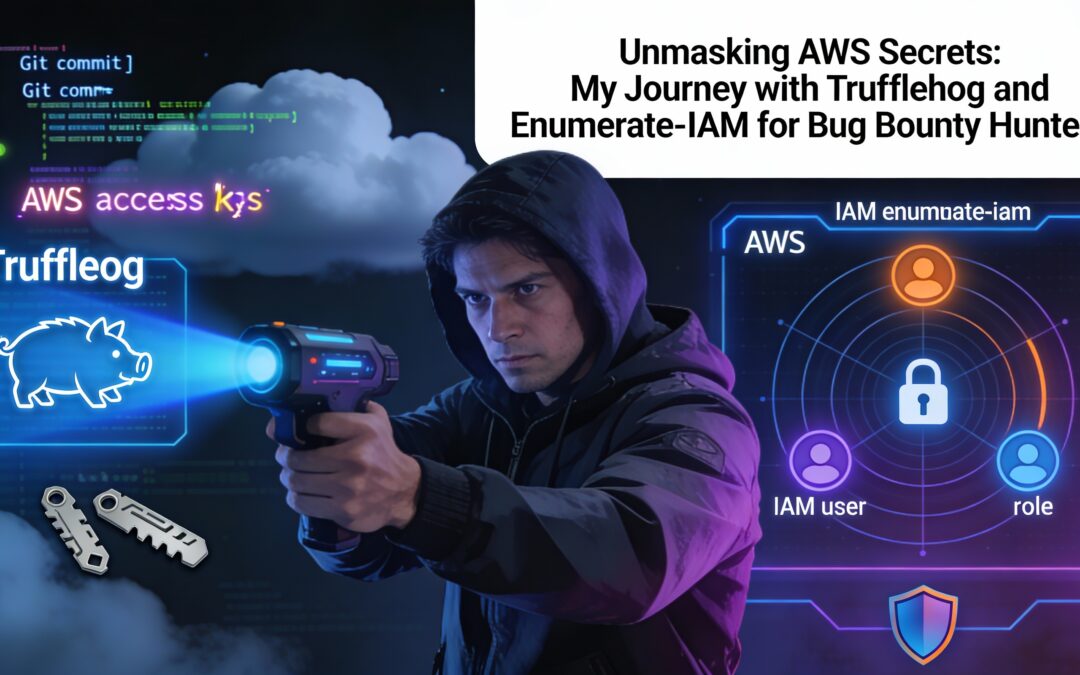
by Royal Cloud | Dec 20, 2025 | Cloud
Are you a bug bounty hunter on a mission to uncover vulnerabilities and secrets hidden within Amazon Web Services (AWS)? In the world of cybersecurity, AWS is a treasure trove for potential security issues, and today, I want to share my journey of discovery using two...
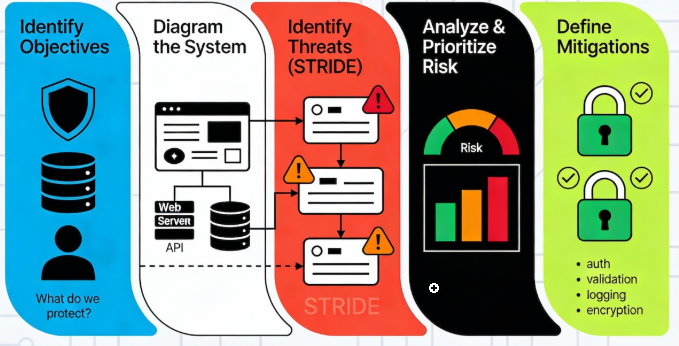
by Royal Cloud | Dec 20, 2025 | Artificial Intelligence (AI)
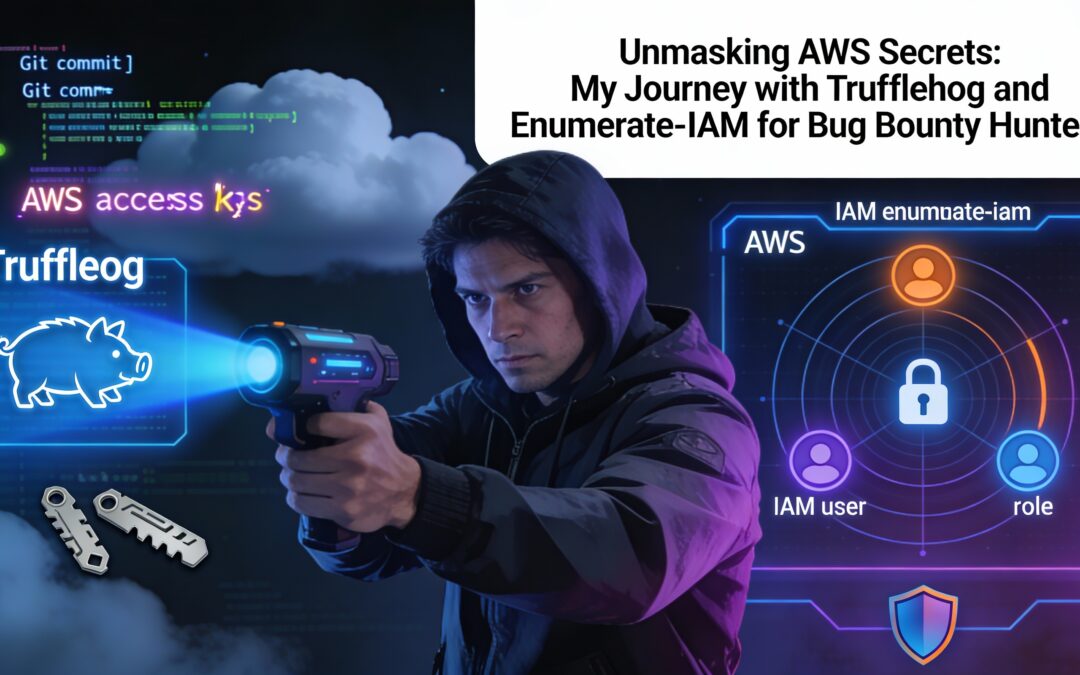
In this article, you’ll discover: · Why threat modeling is essential to any secure development lifecycle (SDLC) · How to move from reactive to proactive security · A deep dive into the SolarWinds attack and how threat modeling could have identified the weaknesses ·...
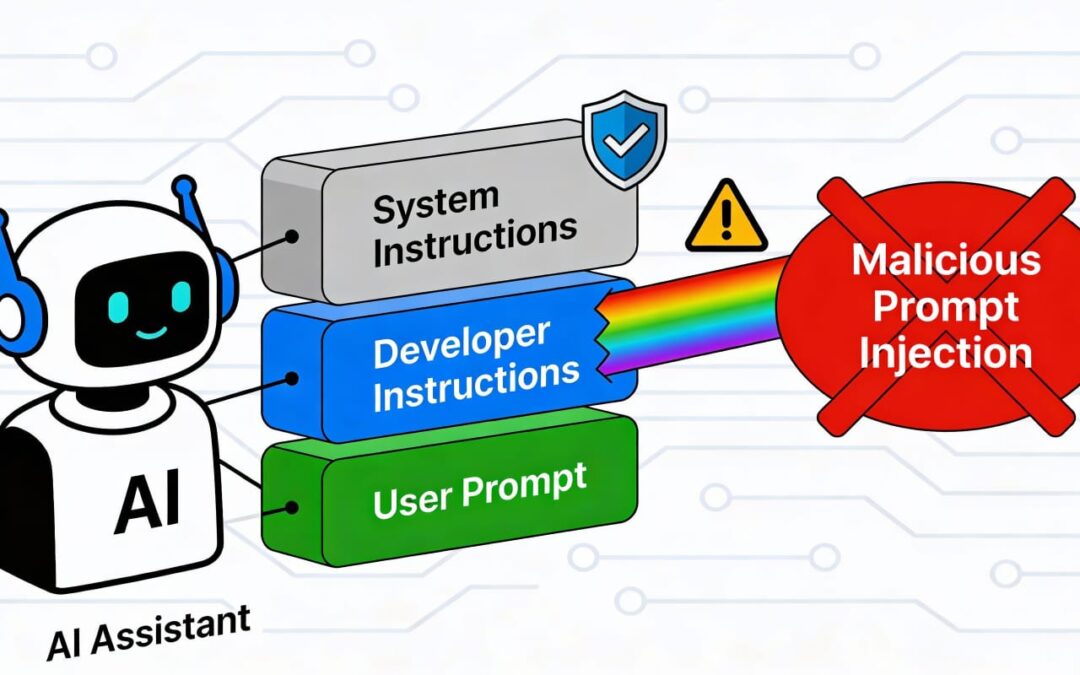
by Royal Cloud | Dec 16, 2025 | Artificial Intelligence (AI)
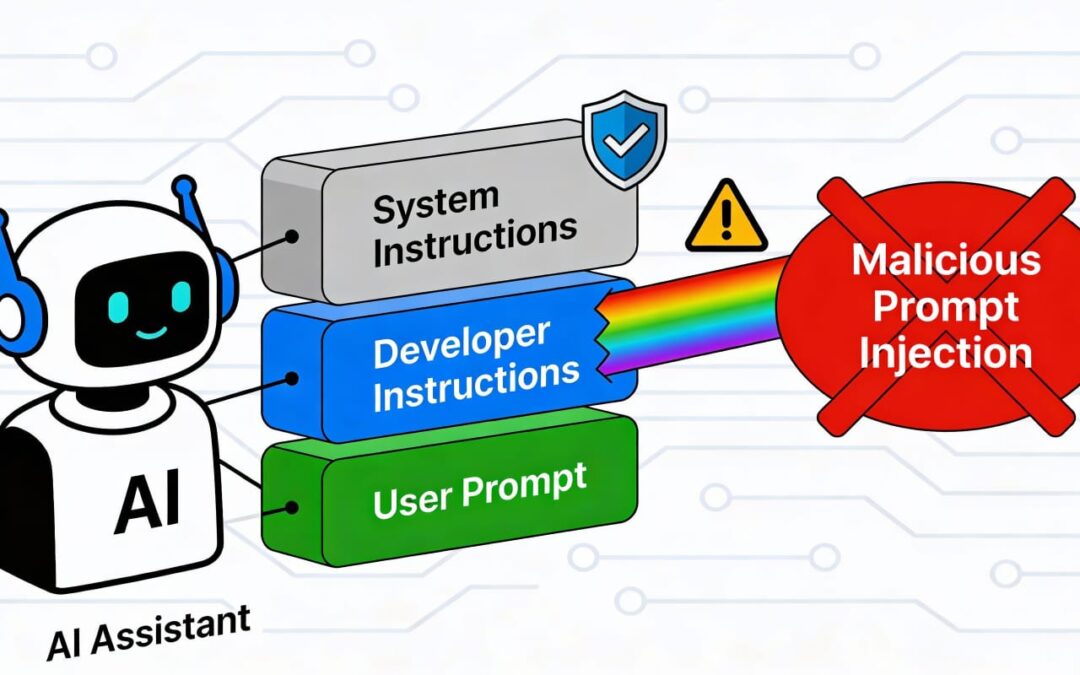
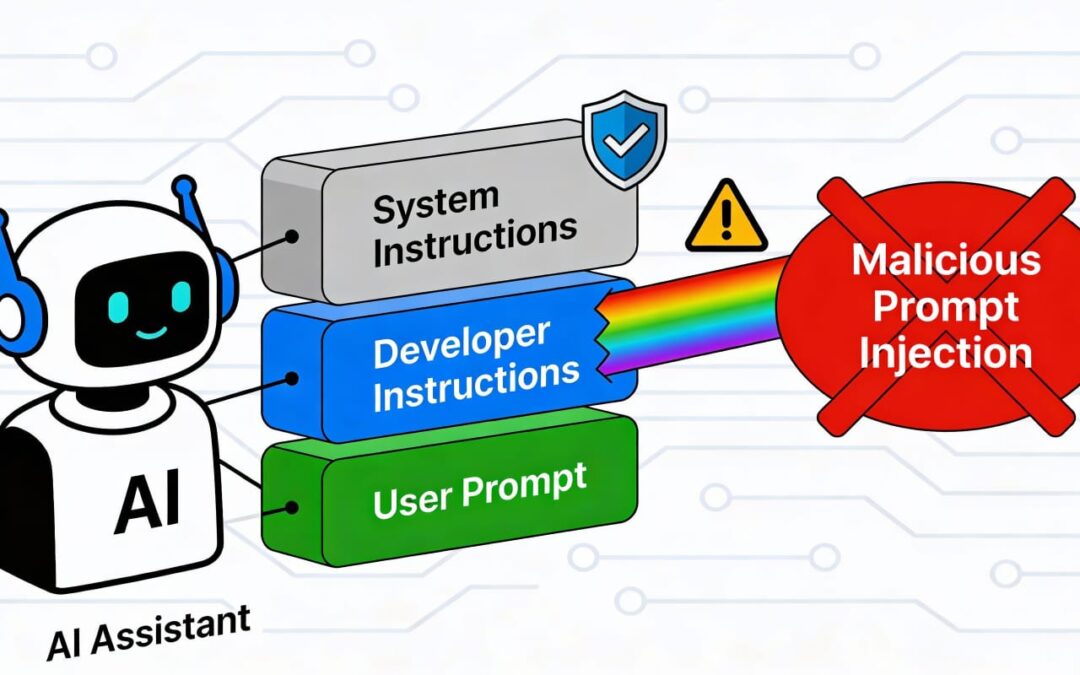
Prompt Injection refers to the act of manipulating or altering the behavior of AI systems by crafting specific inputs (prompts) that exploit vulnerabilities in how the system processes text. Prompt injection can take two primary forms: direct and indirect. 1....
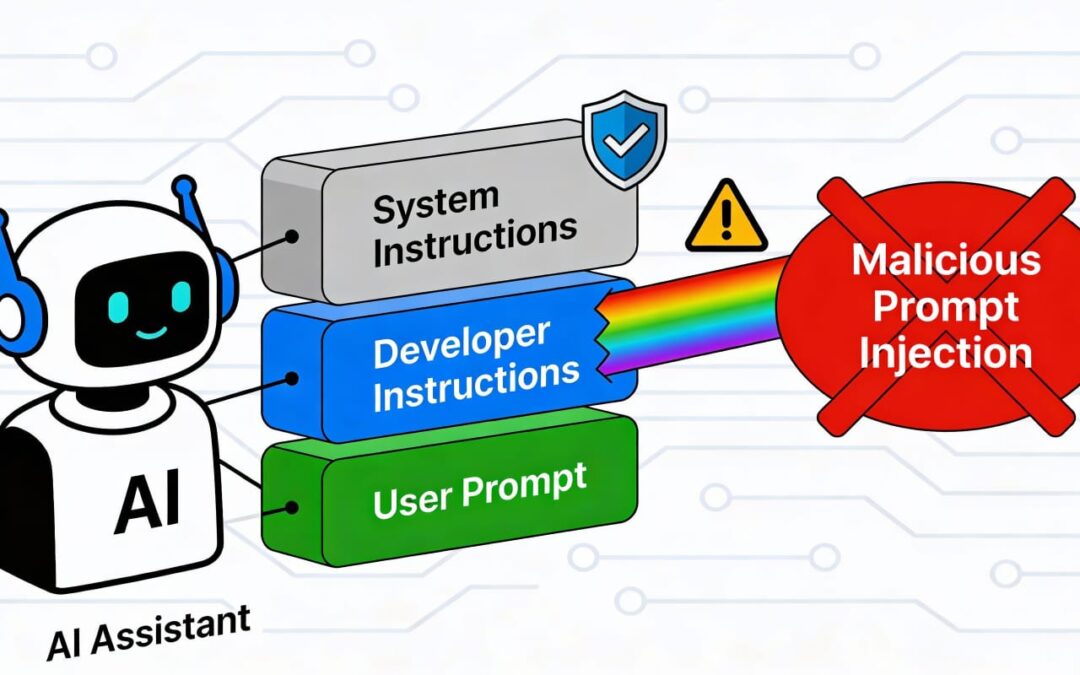
by Royal Cloud | Dec 16, 2025 | Cloud
Prompt injection is a vulnerability that targets artificial intelligence (AI) models, particularly those trained in natural language processing (NLP) and large language models (LLMs). By crafting carefully designed inputs, attackers can manipulate AI systems to behave...