In this article, you’ll discover:
- · Why threat modeling is essential to any secure development lifecycle (SDLC)
- · How to move from reactive to proactive security
- · A deep dive into the SolarWinds attack and how threat modeling could have identified the weaknesses
- · How to apply lessons learned to your own apps and pipelines
⚠️ Haven’t seen Part 1 yet? Make sure to watch it first to get a solid foundation on Threat Modeling, assets, attackers, and how to start thinking like a threat modeler.
Why Is Threat Modeling Important?
From Reactive to Proactive Security
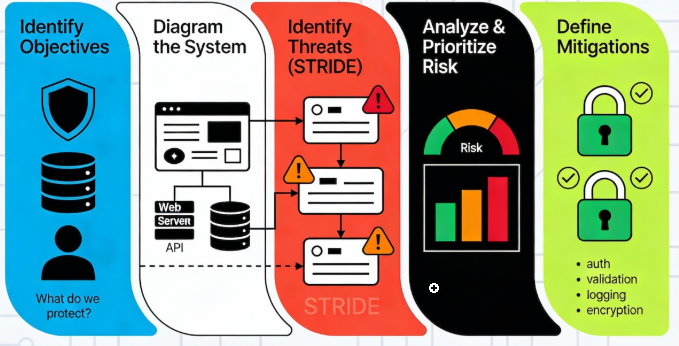
Traditional security approaches often resemble reactive crisis management — scrambling after damage is done. Threat modeling revolutionizes this dynamic by:
1. Preemptively Foreseeing Vulnerabilities
· Identifying attack paths during design allows forewarning of risks
· Mapping weaknesses proactively safeguards before use
· Crafting security blueprints rather than putting out fires
2. Cost-Effectively Mitigating Danger
· Fixing flaws at inception is far cheaper than retrofitting (as IBM Security found)
· Reducing time to spot and respond to incidents
· Lowering insurance premiums via clear safeguard implementation
3. Ensuring Compliance and Accountability
· Meeting regulatory mandates (such as NIST and ISO 27001)
· Documenting due care for legal protection
· Creating auditable records of security considerations
4. The Tangible Benefits of Threat Modeling
· Quantifiable advantages that warrant investment:
5. Risk Reduction Metrics:
· 60–80% decrease in critical vulnerabilities (per Microsoft SDL)
· 40% fall in security incidents (per Forrester Research)
· 90% swifter vulnerability resolution (from a Ponemon Institute study)

An In-Depth Look: The SolarWinds Intrusion (2020)
Attack Anatomy and its Impact
The SolarWinds breach stands as one of history’s most cunning supply chain attacks:
Timeline of Events:
1. Initial Compromise (September 2019): Attackers infiltrated SolarWinds’ systems
2. Implanted Malware: Hijacked Orion platform updates with Sunburst backdoor
3. Widespread Distribution (March 2020): Over 18,000 organizations received tainted updates
4. Secondary Infections: High-value targets among US government agencies impacted

Consequences:
· Estimated global damages exceeding $100 billion
· Compromise of multiple Fortune 500 companies
· National security implications across 9 US federal agencies
· Lasting erosion of trust in software supply chains
· How Threat Modeling Could Have Prevented the Breach.

A thorough threat model would have addressed critical gaps:
1. Supply Chain Visibility
· Would have mapped all third-party dependencies
· Identified update mechanisms as high-risk components
· Enforced stricter vendor security standards
2. Build Process Security
· Implemented multi-person code review requirements
· Established segregated build environments
· Enforced cryptographic signing of all releases
3. Anomaly Detection
· Would have monitored for unusual build activities
· Flagged unexpected network connections
· Detected unauthorized code modifications
4. Defense-in-Depth Controls
· Network segmentation would have contained the breach
· Privileged access management could have limited lateral movement
· Behavioral analytics might have detected attacker reconnaissance.

The SolarWinds assault illustrates the disastrous results of dismissing proactive security measures. Organizations that fall flat to receive danger modeling:
Conclusion: Threat Modeling as a Strategic Necessity
The High Cost of Doing Nothing
- Stay helpless to preventable assaults
• Confront exponentially higher breach costs
• Endure enduring reputational harm
• Risk regulatory punishments and claims.

Thanks for Reading — Let’s Continue the Conversation in Part3!
If you found this article helpful, drop a like or leave a comment — your feedback helps shape future content!
💬 What threat modeling technique do you use most often? Share your thoughts below — let’s learn from each other!
▶️ Want to see real-world examples in action?
Watch the full companion video on Udemy :
https://www.udemy.com/course/master-stride-threat-modeling-hack-proof-your-apps/?couponCode=LEARNNOWPLANS